Recognition: unknown
Hiding Secrets in the CSI Quotient: A Robust Wi-Fi CSI Steganography System
Pith reviewed 2026-05-09 23:59 UTC · model grok-4.3
The pith
Wi-Fi steganography embeds secrets in the quotient of consecutive CSI measurements to remain effective amid environmental changes.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
By computing the quotient of two consecutive CSI vectors, the natural channel response is removed and only the artificial FIR filter components that carry the secret remain. An encoder-decoder neural network is trained to generate the filters at the transmitter and reconstruct the secret at the receiver, yielding both higher embedding rates and reliable recovery even when the environment varies.
What carries the argument
The CSI quotient obtained by dividing one channel state information measurement by the preceding one, which isolates the artificial FIR modifications from the unknown natural propagation effects.
If this is right
- The system continues to work when the surrounding environment changes between transmissions.
- Steganographic capacity increases compared with earlier CSI embedding techniques.
- The modifications remain difficult for an eavesdropper to distinguish from ordinary channel effects.
- Implementation on commercial off-the-shelf hardware confirms practical feasibility.
Where Pith is reading between the lines
- The quotient technique could be applied to other radio systems that provide repeated channel estimates, such as 5G or Bluetooth, if similar FIR-style modifications are feasible.
- Training the neural network on site-specific channel data might further reduce error rates in fixed installations.
- If the added computational cost at the receiver stays low, the method could be integrated into existing Wi-Fi firmware without protocol changes.
Load-bearing premise
Dividing two consecutive CSI measurements cleanly removes the natural wireless channel response without leaving residual leakage or losing the embedded secret under typical multipath conditions.
What would settle it
Measuring secret recovery error rates while deliberately varying the multipath profile between the two CSI snapshots, for example by moving a reflector at different speeds during the interval.
Figures










read the original abstract
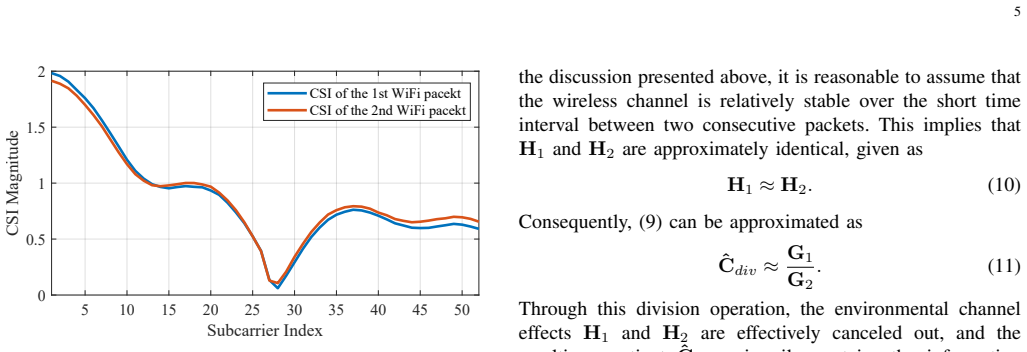
Physical layer (PHY) steganography conceals secrets by making subtle modifications to transmitted radio waveforms, which can be applied to establish covert communication systems. Given the widespread deployment of Wi-Fi infrastructures, hiding secrets within Wi-Fi transmissions exhibits significant covertness and has attracted increasing research attention. Recent advances in Wi-Fi steganography have focused on embedding secrets within channel state information (CSI) by applying artificial finite impulse response (FIR) filters to outgoing signals. These methods can emulate natural wireless propagation effects, thereby evading detection by eavesdroppers. However, existing CSI-based approaches suffer from two critical limitations: vulnerability to environmental variations and limited steganographic capacity. This work presents a Wi-Fi steganography system that mitigates these constraints. Specifically, we introduce a CSI division mechanism to decouple artificial CSI components from natural wireless channel responses. In essence, secrets are embedded within the quotient of two consecutive CSI measurements. Furthermore, we propose an encoder-decoder neural network framework that automatically learns optimal strategies for FIR filter generation and secret recovery, substantially enhancing steganographic capacity. We implemented a prototype using commercial off-the-shelf hardware, including a software-defined radio (SDR) transmitter and two receiver platforms: ANTSDR and ESP32. Experimental evaluations demonstrate that the system achieves robust performance under dynamic environmental conditions while significantly improving steganographic capacity.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper proposes a Wi-Fi physical-layer steganography system that embeds secret data by applying artificial FIR filters to transmitted signals and recovers them from the quotient of two consecutive CSI measurements. An encoder-decoder neural network is used to learn optimal FIR generation and secret extraction strategies. A prototype is implemented on commercial hardware (SDR transmitter with ANTSDR and ESP32 receivers), with experimental claims of robustness under dynamic environmental conditions and substantially higher steganographic capacity than prior CSI-based methods.
Significance. If the robustness and capacity claims can be substantiated with quantitative evidence, the work would offer a practical advance in covert communications by addressing the environmental sensitivity and capacity limits of existing Wi-Fi CSI steganography techniques, leveraging ubiquitous infrastructure for potentially undetectable data hiding.
major comments (2)
- [Abstract] Abstract: The CSI division mechanism is presented as cleanly decoupling artificial FIR-induced components from natural wireless channel responses. This construction yields a quotient equal to (H_artificial * H_natural2) / H_natural1; when the interval between consecutive CSI soundings is not << coherence time, the ratio H_natural2/H_natural1 introduces uncontrolled multiplicative distortion that is neither bounded nor analyzed in the manuscript.
- [Experimental evaluations] Experimental evaluations: The abstract states that prototype experiments demonstrate robust performance under dynamic conditions and significantly improved capacity, yet no quantitative metrics (BER, achievable rate, error bars), baseline comparisons, training-data descriptions, or network hyperparameters are supplied, rendering the central claims unverifiable from the provided text.
minor comments (1)
- [Abstract] The abstract refers to 'significantly improving steganographic capacity' without defining the prior baseline or reporting the numerical improvement factor.
Simulated Author's Rebuttal
We thank the referee for the constructive feedback on our manuscript. We address each major comment point by point below, indicating the revisions we will incorporate to improve clarity and substantiation of our claims.
read point-by-point responses
-
Referee: [Abstract] Abstract: The CSI division mechanism is presented as cleanly decoupling artificial FIR-induced components from natural wireless channel responses. This construction yields a quotient equal to (H_artificial * H_natural2) / H_natural1; when the interval between consecutive CSI soundings is not << coherence time, the ratio H_natural2/H_natural1 introduces uncontrolled multiplicative distortion that is neither bounded nor analyzed in the manuscript.
Authors: The referee accurately notes the mathematical expression of the quotient. Our system design selects CSI sounding intervals short enough relative to typical indoor coherence times (on the order of tens of milliseconds) so that H_natural2/H_natural1 remains close to unity. The end-to-end neural network is trained to extract secrets robustly in the presence of residual variations. We agree, however, that an explicit bound on the distortion term and its impact on bit-error rate was not derived or simulated in the original manuscript. In the revised version we will add a dedicated analysis subsection with both theoretical bounds under Rayleigh fading assumptions and supporting Monte-Carlo results. revision: yes
-
Referee: [Experimental evaluations] Experimental evaluations: The abstract states that prototype experiments demonstrate robust performance under dynamic conditions and significantly improved capacity, yet no quantitative metrics (BER, achievable rate, error bars), baseline comparisons, training-data descriptions, or network hyperparameters are supplied, rendering the central claims unverifiable from the provided text.
Authors: We acknowledge that the experimental section in the submitted manuscript did not present the quantitative results with sufficient detail. The revised manuscript will include explicit BER curves versus SNR and environmental dynamics, capacity comparisons against prior CSI-based steganography schemes, error bars computed over repeated trials, a description of the training dataset (synthetic channels generated from the 3GPP model plus real CSI traces collected in our lab), and the full encoder-decoder architecture together with all training hyperparameters. Additional baseline experiments using conventional FIR design without the neural network will also be added for completeness. revision: yes
Circularity Check
No circularity in experimental CSI quotient steganography system
full rationale
The paper describes a prototype system that embeds secrets in the quotient of consecutive CSI measurements and recovers them via a trained encoder-decoder network. No mathematical derivations, first-principles predictions, or equations are presented that reduce to fitted parameters or self-citations by construction. The central claims rest on hardware implementation and experimental evaluations under dynamic conditions, which are independent of the target results. No load-bearing self-citations, uniqueness theorems, or ansatzes are invoked in the abstract or description.
Axiom & Free-Parameter Ledger
Reference graph
Works this paper leans on
-
[1]
Physical layer covert communication in B5G wireless networks—its research, applications, and challenges,
Y . Jiang, L. Wang, H.-H. Chen, and X. Shen, “Physical layer covert communication in B5G wireless networks—its research, applications, and challenges,”Proc. IEEE, vol. 112, pp. 47–82, 2024
2024
-
[2]
SteaLTE: Private 5G cellular connectivity as a service with full-stack wireless steganography,
L. Bonati, S. D’Oro, F. Restuccia, S. Basagni, and T. Melodia, “SteaLTE: Private 5G cellular connectivity as a service with full-stack wireless steganography,” inProc. IEEE Int. Conf. Comput. Commun. (INFO- COM), 2021, pp. 1–10
2021
-
[3]
Hiding data in plain sight: Un- detectable wireless communications through pseudo-noise asymmetric shift keying,
S. D’Oro, F. Restuccia, and T. Melodia, “Hiding data in plain sight: Un- detectable wireless communications through pseudo-noise asymmetric shift keying,” inProc. IEEE Int. Conf. Comput. Commun. (INFOCOM), 2019, pp. 1585–1593
2019
-
[4]
Covert communications: A comprehensive survey,
X. Chen, J. An, Z. Xiong, C. Xing, N. Zhao, F. R. Yu, and A. Nal- lanathan, “Covert communications: A comprehensive survey,”IEEE Commun. Surveys Tuts., vol. 25, pp. 1173–1198, 2023
2023
-
[5]
No time for remodulation: A PHY steganographic symbiotic channel over constant envelope,
J. Liu, C. Du, J. Yu, J. Liu, and H. Qi, “No time for remodulation: A PHY steganographic symbiotic channel over constant envelope,”IEEE Trans. Inf. Forensics Security, vol. 20, pp. 2197–2211, 2025
2025
-
[6]
LoPhy: A resilient and fast covert channel over LoRa PHY,
B. Liu, C. Gu, S. He, and J. Chen, “LoPhy: A resilient and fast covert channel over LoRa PHY,” inProc. Int. Conf. Inf. Process. Sensor Netw. (IPSN), 2023, pp. 1–13
2023
-
[7]
CloakLoRa: A covert channel over LoRa PHY,
N. Hou, X. Xia, and Y . Zheng, “CloakLoRa: A covert channel over LoRa PHY,”IEEE/ACM Trans. Netw., vol. 31, no. 3, pp. 1159–1172, 2022
2022
-
[8]
Practical covert channels for WiFi systems,
J. Classen, M. Schulz, and M. Hollick, “Practical covert channels for WiFi systems,” inProc. IEEE Conf. Commun. Net. Secur. (CNS), 2015, pp. 209–217
2015
-
[9]
A survey on wireless security: Technical challenges, recent advances, and future trends,
Y . Zou, J. Zhu, X. Wang, and L. Hanzo, “A survey on wireless security: Technical challenges, recent advances, and future trends,”Proc. IEEE, vol. 104, no. 9, pp. 1727–1765, 2016
2016
-
[10]
Exploiting frame preamble waveforms to support new physical-layer functions in OFDM-based 802.11 systems,
H. Rahbari and M. Krunz, “Exploiting frame preamble waveforms to support new physical-layer functions in OFDM-based 802.11 systems,” IEEE Trans. Wireless Commun., vol. 16, no. 6, pp. 3775–3786, 2017
2017
-
[11]
Adaptive preamble embedding with MIMO to support user-defined functionalities in WLANs,
Z. Zhang, H. Rahbari, and M. Krunz, “Adaptive preamble embedding with MIMO to support user-defined functionalities in WLANs,”IEEE Trans. Mobile Comput., vol. 22, no. 2, pp. 691–707, 2021
2021
-
[12]
WISE: Waveform independent signal embedding for covert communication,
X. Wei and D. Saha, “WISE: Waveform independent signal embedding for covert communication,”IEEE Trans. Mach. Learn. Commun. Netw., vol. 2, pp. 64–80, 2024
2024
-
[13]
Shadow Wi-Fi: Teaching smartphones to transmit raw signals and to extract channel state information to implement practical covert channels over Wi-Fi,
M. Schulz, J. Link, F. Gringoli, and M. Hollick, “Shadow Wi-Fi: Teaching smartphones to transmit raw signals and to extract channel state information to implement practical covert channels over Wi-Fi,” inProc. Int. Conf. Mobile Syst. Appl. Services (MobiSys), 2018, pp. 256–268
2018
-
[14]
Openwifi CSI fuzzer for authorized sensing and covert channels,
X. Jiao, M. Mehari, W. Liu, M. Aslam, and I. Moerman, “Openwifi CSI fuzzer for authorized sensing and covert channels,” inProc. Conf. Secur. Privacy in Wireless and Mobile Networks (WiSec), 2021, pp. 377–379
2021
-
[15]
MATLAB WLAN toolbox,
MathWorks, “MATLAB WLAN toolbox,” https://www.mathworks.com/ products/wlan.html, accessed: 2025-06-23
2025
-
[16]
openwifi: a free and open-source IEEE802.11 SDR implementation on SoC,
X. Jiao, W. Liu, M. Mehari, M. Aslam, and I. Moerman, “openwifi: a free and open-source IEEE802.11 SDR implementation on SoC,” in Proc. IEEE Veh. Technol. Conf. (VTC-Spring), 2020, pp. 1–2
2020
-
[17]
OpenWiFi project,
X. Jiao, “OpenWiFi project,” https://github.com/open-sdr/openwifi, ac- cessed: 2025-06-23
2025
-
[18]
ESP-CSI project,
Espressif Systems, “ESP-CSI project,” https://github.com/espressif/ esp-csi, accessed: 2025-06-23
2025
-
[19]
Enhancing BER performance limit of BCH and RS codes using multipath diversity,
A. Al-Barrak, A. Al-Sherbaz, T. Kanakis, and R. Crockett, “Enhancing BER performance limit of BCH and RS codes using multipath diversity,” Computers, vol. 6, no. 2, p. 21, 2017
2017
-
[20]
Efficient key gen- eration by exploiting randomness from channel responses of individual OFDM subcarriers,
J. Zhang, A. Marshall, R. Woods, and T. Q. Duong, “Efficient key gen- eration by exploiting randomness from channel responses of individual OFDM subcarriers,”IEEE Trans. Commun., vol. 64, no. 6, pp. 2578– 2588, 2016
2016
-
[21]
Intelligent reflecting surface enabled covert communications in wireless networks,
X. Lu, E. Hossain, T. Shafique, S. Feng, H. Jiang, and D. Niyato, “Intelligent reflecting surface enabled covert communications in wireless networks,”IEEE Network, vol. 34, no. 5, pp. 148–155, 2020
2020
-
[22]
Intelligent reflecting surface- assisted multi-antenna covert communications: Joint active and passive beamforming optimization,
C. Wang, Z. Li, J. Shi, and D. W. K. Ng, “Intelligent reflecting surface- assisted multi-antenna covert communications: Joint active and passive beamforming optimization,”IEEE Trans. Commun., vol. 69, no. 6, pp. 3984–4000, 2021
2021
-
[23]
Intelligent reflecting surface (IRS)-aided covert wireless communications with delay constraint,
X. Zhou, S. Yan, Q. Wu, F. Shu, and D. W. K. Ng, “Intelligent reflecting surface (IRS)-aided covert wireless communications with delay constraint,”IEEE Trans. Wireless Commun., vol. 21, no. 1, pp. 532–547, 2021
2021
-
[24]
Covert communication assisted by UA V-IRS,
C. Wang, X. Chen, J. An, Z. Xiong, C. Xing, N. Zhao, and D. Niyato, “Covert communication assisted by UA V-IRS,”IEEE Trans. Commun., vol. 71, no. 1, pp. 357–369, 2022
2022
-
[25]
Covert communications via two-way IRS with noise power uncertainty,
C. Wang, Z. Xiong, M. Zheng, N. Zhao, and D. Niyato, “Covert communications via two-way IRS with noise power uncertainty,”IEEE Trans. Commun., vol. 72, no. 8, pp. 4803–4815, 2024
2024
-
[26]
IRS-assisted covert communication with equal and unequal transmit prior probabilities,
Y . Wu, X. Chen, M. Liu, L. Xu, N. Zhao, X. Wang, and D. W. K. Ng, “IRS-assisted covert communication with equal and unequal transmit prior probabilities,”IEEE Trans. Commun., vol. 72, no. 5, pp. 2897– 2912, 2023
2023
-
[27]
Multi-antenna jamming in covert communication,
O. Shmuel, A. Cohen, and O. Gurewitz, “Multi-antenna jamming in covert communication,”IEEE Trans. Commun., vol. 69, no. 7, pp. 4644– 4658, 2021
2021
-
[28]
Performance analysis and optimization for jammer-aided multiantenna UA V covert communication,
H. Du, D. Niyato, Y .-A. Xie, Y . Cheng, J. Kang, and D. I. Kim, “Performance analysis and optimization for jammer-aided multiantenna UA V covert communication,”IEEE J. Sel. Areas Commun., vol. 40, no. 10, pp. 2962–2979, 2022
2022
-
[29]
Multi-antenna covert communications in random wireless networks,
T.-X. Zheng, H.-M. Wang, D. W. K. Ng, and J. Yuan, “Multi-antenna covert communications in random wireless networks,”IEEE Trans. Wireless Commun., vol. 18, no. 3, pp. 1974–1987, 2019
1974
-
[30]
Wireless covert communications aided by distributed cooperative jamming over slow fading channels,
T.-X. Zheng, Z. Yang, C. Wang, Z. Li, J. Yuan, and X. Guan, “Wireless covert communications aided by distributed cooperative jamming over slow fading channels,”IEEE Trans. Wireless Commun., vol. 20, no. 11, pp. 7026–7039, 2021
2021
-
[31]
Covert communication over adversarially jammed channels,
Q. Zhang, M. Bakshi, and S. Jaggi, “Covert communication over adversarially jammed channels,”IEEE Trans. Inf. Theory, vol. 67, no. 9, pp. 6096–6121, 2021. 12
2021
-
[32]
Jamming aided covert com- munication with multiple receivers,
K.-W. Huang, H. Deng, and H.-M. Wang, “Jamming aided covert com- munication with multiple receivers,”IEEE Trans. Wireless Commun., vol. 20, no. 7, pp. 4480–4494, 2021
2021
-
[33]
Covert communi- cation of multi-antenna af relaying networks,
Q. Jin, L. Fan, X. Lei, J. Zhao, and A. Nallanathan, “Covert communi- cation of multi-antenna af relaying networks,”IEEE Trans. Commun., 2025
2025
-
[34]
Impairment shift keying: Covert signaling by deep learning of controlled radio imperfections,
K. Sankhe, F. Restuccia, S. D’Oro, T. Jian, Z. Wang, A. Al-Shawabka, J. Dy, T. Melodia, S. Ioannidis, and K. Chowdhury, “Impairment shift keying: Covert signaling by deep learning of controlled radio imperfections,” inProc. IEEE Mil. Commun. Conf. (MILCOM), 2019, pp. 598–603
2019
-
[35]
Secret agent radio: Covert communication through dirty constellations,
A. Dutta, D. Saha, D. Grunwald, and D. Sicker, “Secret agent radio: Covert communication through dirty constellations,” inProc. of Springer Int. Workshop on Information Hiding (IH), 2012, pp. 160–175
2012
-
[36]
Information hiding-a survey,
F. A. Petitcolas, R. J. Anderson, and M. G. Kuhn, “Information hiding-a survey,”Proc. IEEE, vol. 87, no. 7, pp. 1062–1078, 2002
2002
-
[37]
Katzenbeisser and F
S. Katzenbeisser and F. Petitcolas,Information hiding. Artech house, 2016
2016
-
[38]
Hidden: Hiding data with deep networks,
J. Zhu, R. Kaplan, J. Johnson, and F.-F. Li, “Hidden: Hiding data with deep networks,” inProc. European Conf. Comput. Vis. (ECCV), 2018, pp. 657–672
2018
-
[39]
Large-capacity image steganography based on invertible neural networks,
S.-P. Lu, R. Wang, T. Zhong, and P. L. Rosin, “Large-capacity image steganography based on invertible neural networks,” inProc. IEEE Conf. Comput. Vis. Pattern Recognit. (CVPR), 2021, pp. 10 816–10 825
2021
-
[40]
A new high capacity image steganography method combined with image elliptic curve cryptography and deep neural network,
X. Duan, D. Guo, N. Liu, B. Li, M. Gou, and C. Qin, “A new high capacity image steganography method combined with image elliptic curve cryptography and deep neural network,”IEEE Access, vol. 8, pp. 25 777–25 788, 2020
2020
-
[41]
Steganogan: High capacity image steganography with gans,
K. A. Zhang, A. Cuesta-Infante, and K. Veeramachaneni, “SteganoGAN: High capacity image steganography with GANs,”arXiv preprint, 2019. [Online]. Available: https://arxiv.org/abs/1901.03892
-
[42]
An embedding cost learning framework using GAN,
J. Yang, D. Ruan, J. Huang, X. Kang, and Y .-Q. Shi, “An embedding cost learning framework using GAN,”IEEE Trans. Inf. Forensics Security, vol. 15, pp. 839–851, 2019
2019
-
[43]
HiNet: Deep image hiding by invertible network,
J. Jing, X. Deng, M. Xu, J. Wang, and Z. Guan, “HiNet: Deep image hiding by invertible network,” inProc. IEEE/CVF Int. Conf. Comput. Vis. (ICCV), 2021, pp. 4733–4742
2021
-
[44]
Hiding images within images,
S. Baluja, “Hiding images within images,”IEEE Trans. Pattern Anal. Mach. Intell., vol. 42, no. 7, pp. 1685–1697, 2019
2019
-
[45]
Information-hiding cameras: Optical concealment of object information into ordinary images,
B. Bai, R. Lee, Y . Li, T. Gan, Y . Wang, M. Jarrahi, and A. Ozcan, “Information-hiding cameras: Optical concealment of object information into ordinary images,”Science Advances, vol. 10, no. 24, 2024
2024
-
[46]
Adversarial watermarking transformer: Towards tracing text provenance with data hiding,
S. Abdelnabi and M. Fritz, “Adversarial watermarking transformer: Towards tracing text provenance with data hiding,” inProc. IEEE Secur. Privacy (S&P), 2021, pp. 121–140
2021
-
[47]
Cross-modal text steganography against synonym substitution-based text attack,
W. Peng, T. Wang, Z. Qian, S. Li, and X. Zhang, “Cross-modal text steganography against synonym substitution-based text attack,”IEEE Signal Process. Lett., vol. 30, pp. 299–303, 2023
2023
-
[48]
RNN-stega: Linguistic steganography based on recurrent neural net- works,
Z.-L. Yang, X.-Q. Guo, Z.-M. Chen, Y .-F. Huang, and Y .-J. Zhang, “RNN-stega: Linguistic steganography based on recurrent neural net- works,”IEEE Trans. Inf. Forensics Security, vol. 14, no. 5, pp. 1280– 1295, 2018
2018
-
[49]
Audio steganography based on iterative adversarial attacks against convolutional neural networks,
J. Wu, B. Chen, W. Luo, and Y . Fang, “Audio steganography based on iterative adversarial attacks against convolutional neural networks,” IEEE Trans. Inf. Forensics Security, vol. 15, pp. 2282–2294, 2020
2020
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.